INTROSPY FOR ANDROID
- Layout for this exercise:
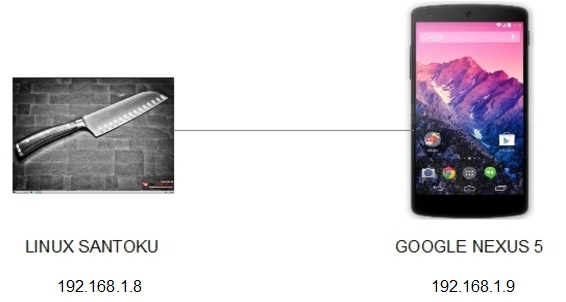
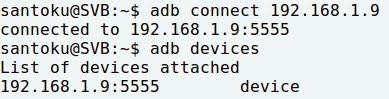
- Connecting Santoku to Nexus 5:
0 - INTRODUCTION
- Introspy-Android is a tool very useful to help understand what an Android application is doing at runtime and assist in the identification of potential security issues.
- It comprises two separate components: a GUI interface to configure hooks, filters and options and a Cydia Substrate extension containing the core of the tool functionalities, including hooks and analysis of potential issues.
- Introspy-Android can be installed on a rooted device and dynamically configured to hook security-sensitive Android API's at run-time.
- The tool records all the relevant API calls made by an application, including function calls, arguments and return values. It then performs tests for security issues in real time and persists the results in a database and in the Android logging system.
- The Introspy-Analyzer can then be used to analyze a database generated by the tracer, and generate HTML reports containing the list of logged function calls as well as a list of potential vulnerabilities affecting the application.
- All components of Introspy can be downloaded from here:
https://github.com/iSECPartners/Introspy-Android
- The installation of Introspy Android comprises of three steps.
1 - INSTALLING SuperSU
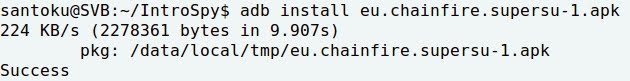
- The first step is to install SuperSu on the mobile device:
http://www.supersu.com/
- SuperSU allows advanced management of Superuser access rights for all the apps on a mobile device that need root privileges.
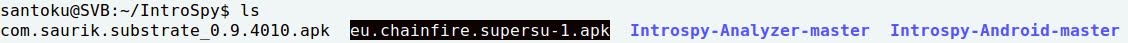
- Installing SuperSU with ADB:

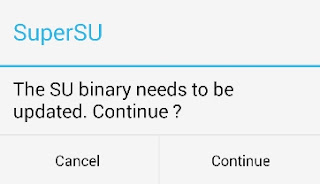
- Clicking Continue to update SuperSU:
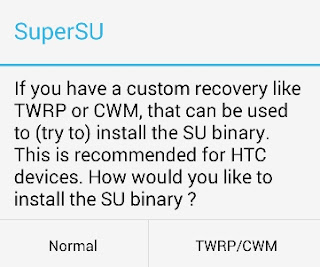
- Normal option:
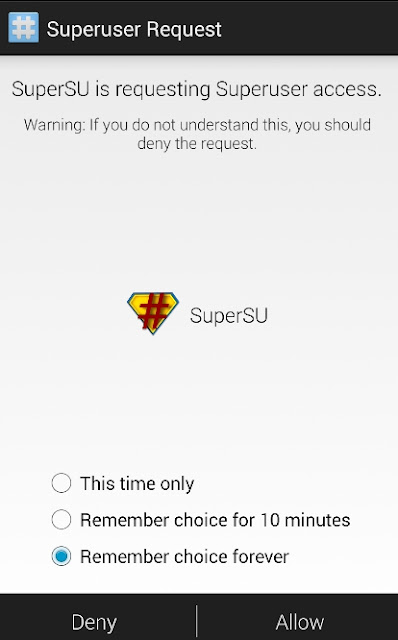
- Allowing access to privileges:
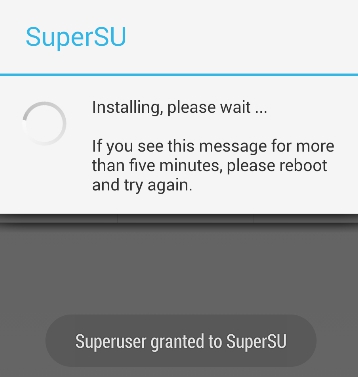
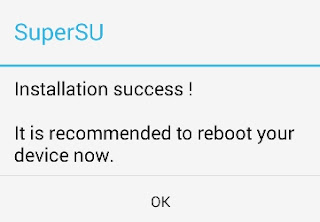
- After the installation, a reboot of the mobile device is advised:
2 - INSTALLING CYDIA SUBSTRATE
- The second step consists of installing Cydia Substrate, what can be downloaded from here:
http://www.cydiasubstrate.com/
-Cydia Substrate is a package manager mobile application that enables a user to find and install software packages on Android devices (of course, also in iOS):
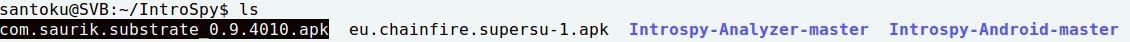
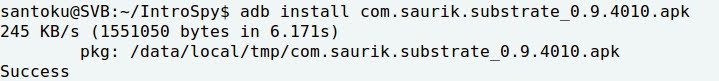
- Installing Cydia Substrate with ADB:
- Clicking the icon for Substrate:
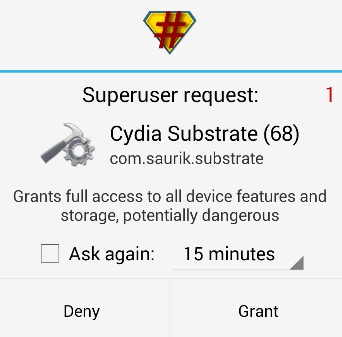
- Linking files and granting superuser permissions to Cydia Substrate:
- Restarting the system (soft):
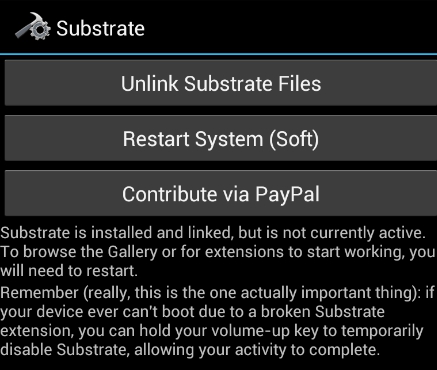

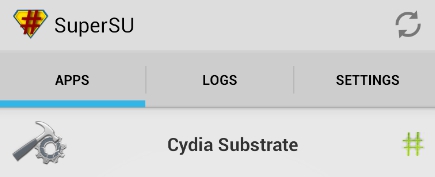
- Now, SuperSU has Cydia Substrate as a linked application:
3 - INSTALLING INTROSPY CORE AND CONFIG
- Introspy has got two applications (Core and Configure) that must be installed separately. Core consists of the API hooking code, whereas Config allows the user to select the application to be analyzed:
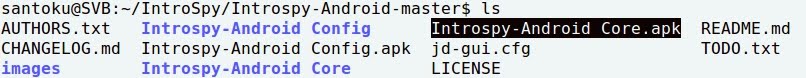
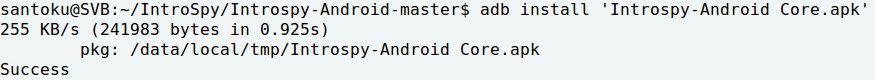
- Installing Introspy-Core (no icon):
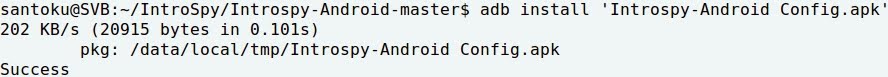
- Installing Introspy-Config:
- Clicking the Introspy-Config icon:

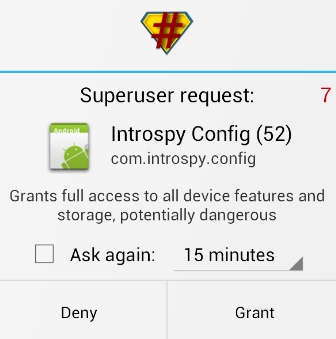
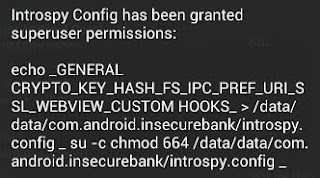
- Granting full access to Introspy-Config:
4 - TESTING INTROSPY ANDROID
- In this exercise we are going to analyze InsecureBank as example, so that option must be selected at the Config list:

- InsecureBank was also used at this exercise.
- Clicking the icon for InsecureBank:

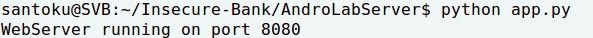
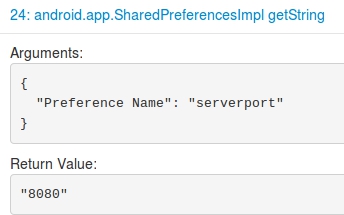
- Running the InsecureBank server on Santoku (192.168.1.8) and listening on port 8080:
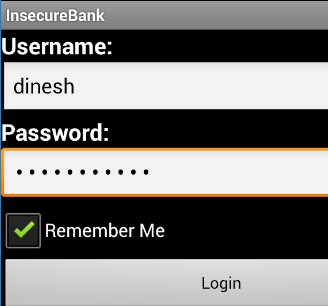
- Starting the application:

- Entering the credentials for InsecureBank (dinesh / dinesh@123$):
- Transferring some money between two accounts:
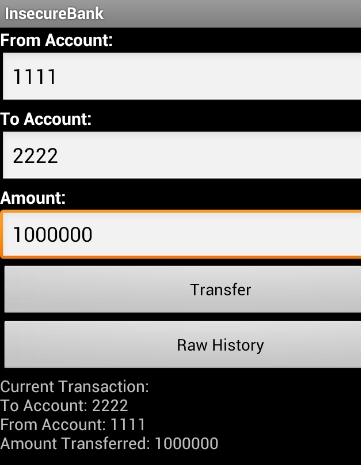
- In the meanwhile we are using InsecureBank, Introspy is gathering information and creating some reports.
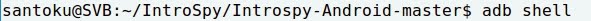
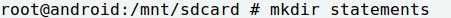
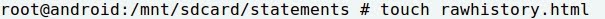
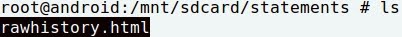
- To access the information created by Introspy a rawhistory.html file is created with ADB:
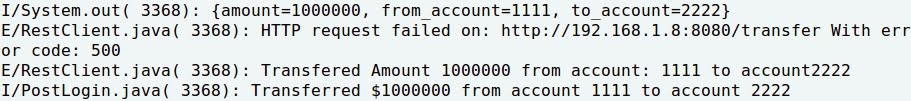
- Enabling logcat, the transfer is displayed:

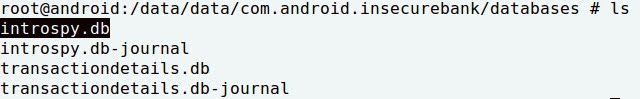
- Now, Introspy has created a couple of databases at the mobile device, the first is called introspy.db:
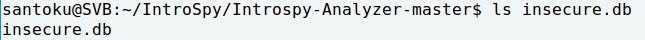
- Pulling with ADB the database insecure.db from the mobile device to Santoku, with the purpose of being analyzed in an HTML format:

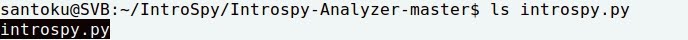
- The Python script introspy.py (-p = platform Android, -o = output InsecureBank), located at the Analyzer folder, creates a file report.html from insecure.db:

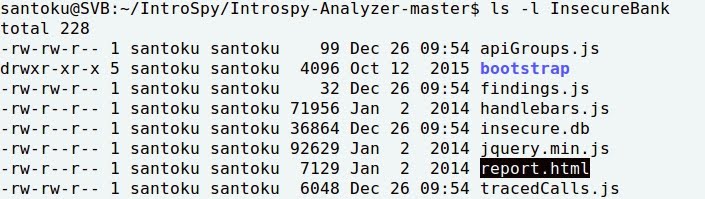
- Going to the newly created folder InsecureBank, there is the report.html:
- Opening report.html with Firefox, a lot of information created by Introspy can be analyzed:

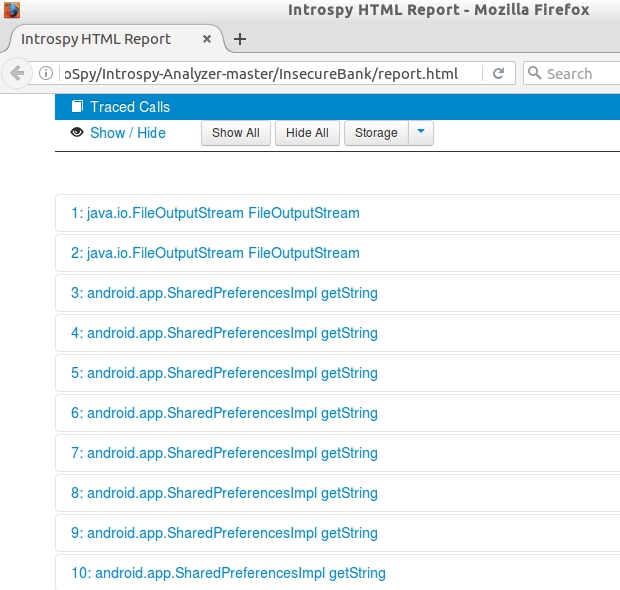
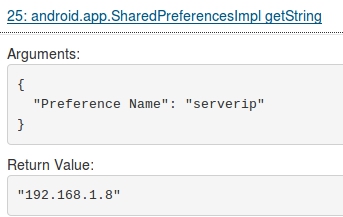
- For instance, going to some Shared Preferences, it can be checked what are the Server and Port used by the application InsecureBank:
- As seen along this exercise, Introspy helps to analyze the APIs called during the usage of the application, what can contribute to detect the vulnerabilities in an automated way.